Validate and prevent drift from security intent
Confirm that code changes align with approved architecture, required security controls, and prior mitigation decisions before they are deployed.
Key Benefits
Increase implementation of required security controls by 4×
Detect and reduce drift from security policies and approved patterns by up to 95%
Key Benefits
Increase implementation of required security controls by 4×
Detect and reduce drift from security policies and approved patterns by up to 95%

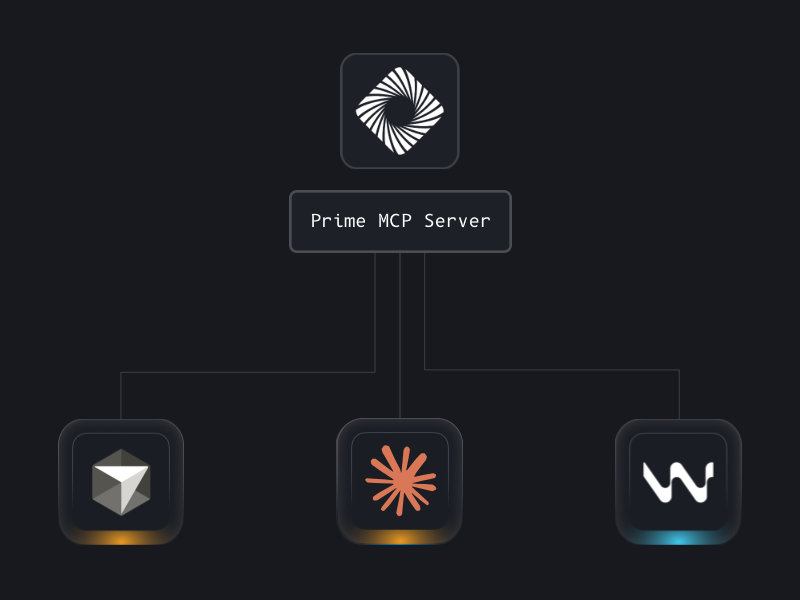
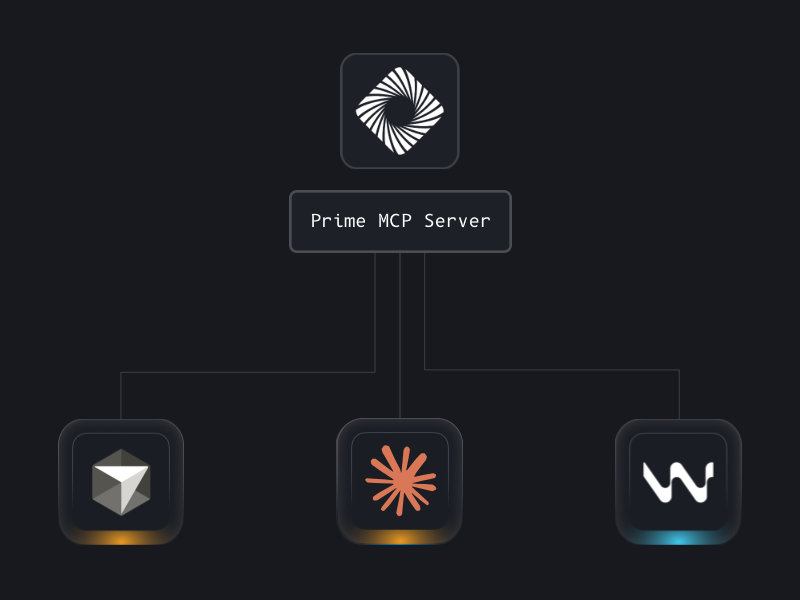
Bring the same security rigor directly into AI dev tools
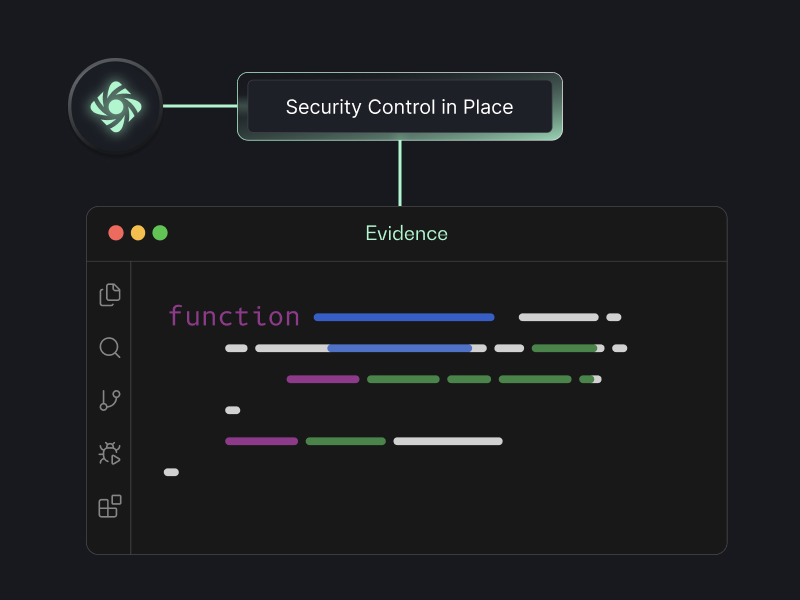
Design to implementation alignment
Map approved design recommendations and required security controls to the relevant implementation
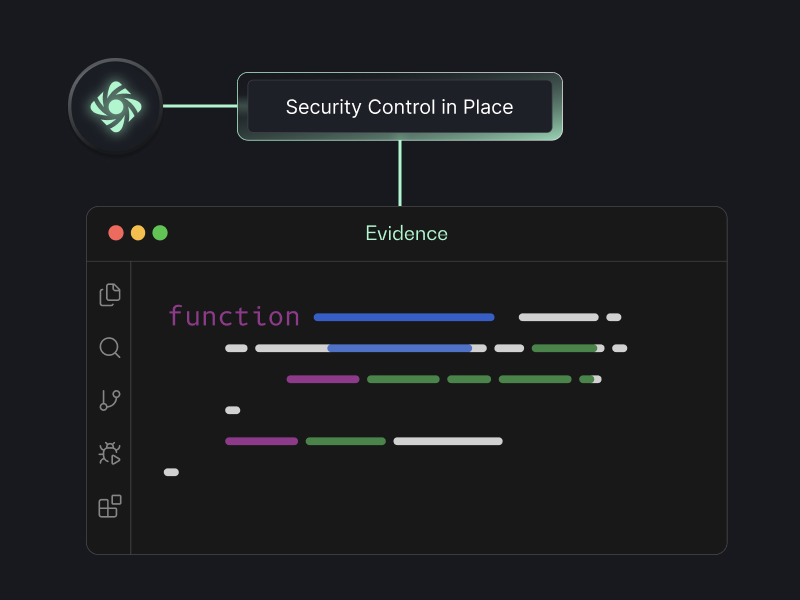
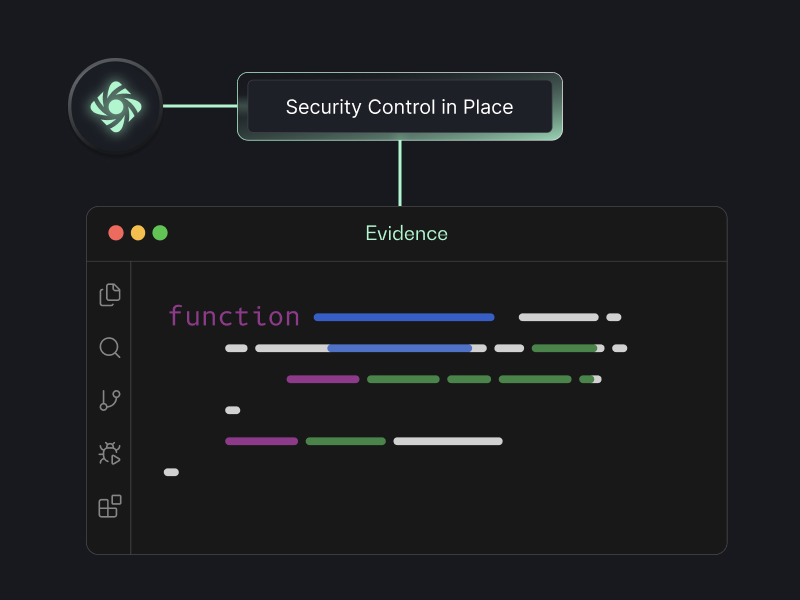
Validation Reasoning
Provide clear reasoning and traceability for how each required control was validated, including where gaps or drift were detected


Continuous control monitoring
Continuously monitor implemented security controls over time to detect changes, drift, or degradation

See Prime Security in Action
Book a demo to see Prime in action



.png)



.png)



