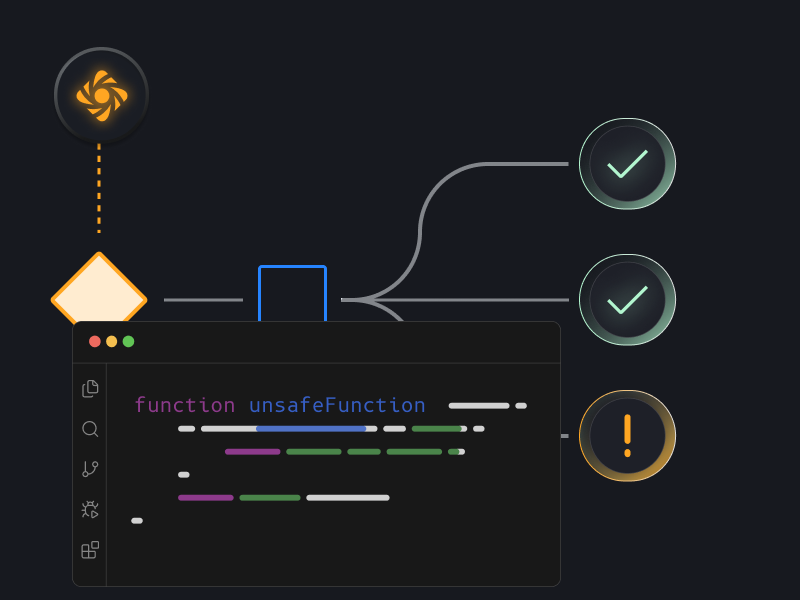
Catch broken security logic before it ships
Review pull requests to ensure security requirements, controls, and critical logic are correctly implemented for PRs and Repos.
Key Benefits
3x improvement in broken security logic
Applies security validation to every pull request before production
Key Benefits
3x improvement in broken security logic
Applies security validation to every pull request before production

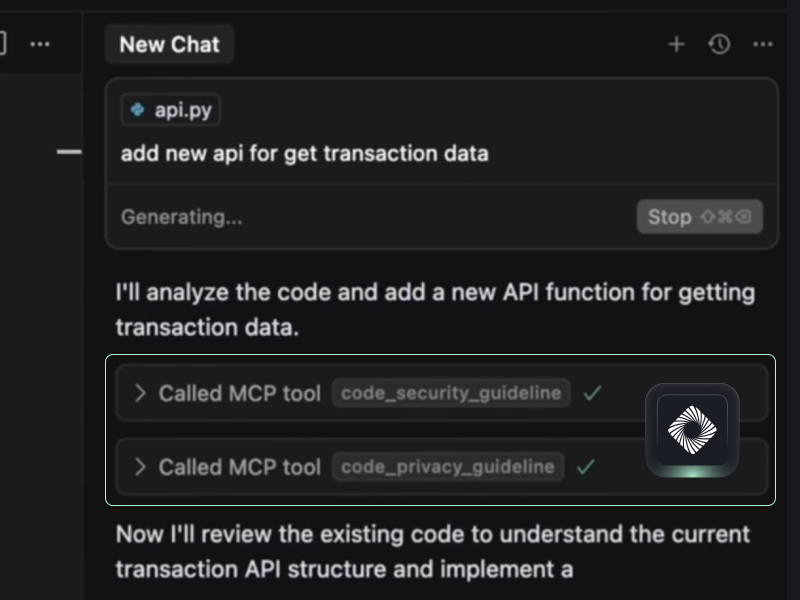
Bring the same security rigor directly into AI dev tools
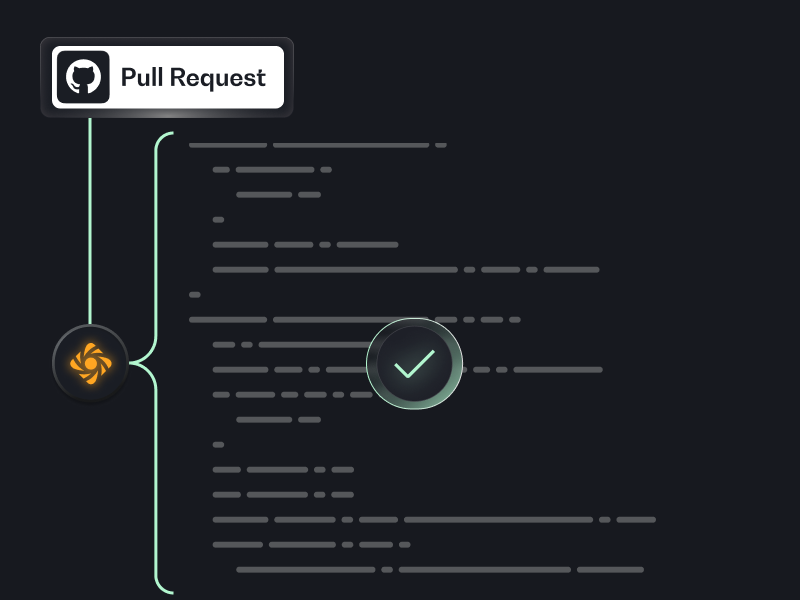
Pull Request Monitoring
Monitor every pull request to ensure every change is evaluated before deployment
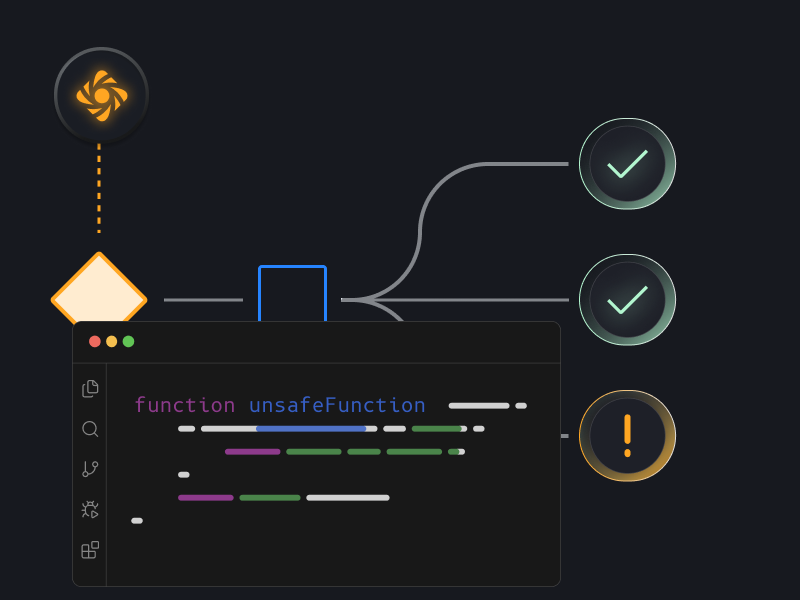
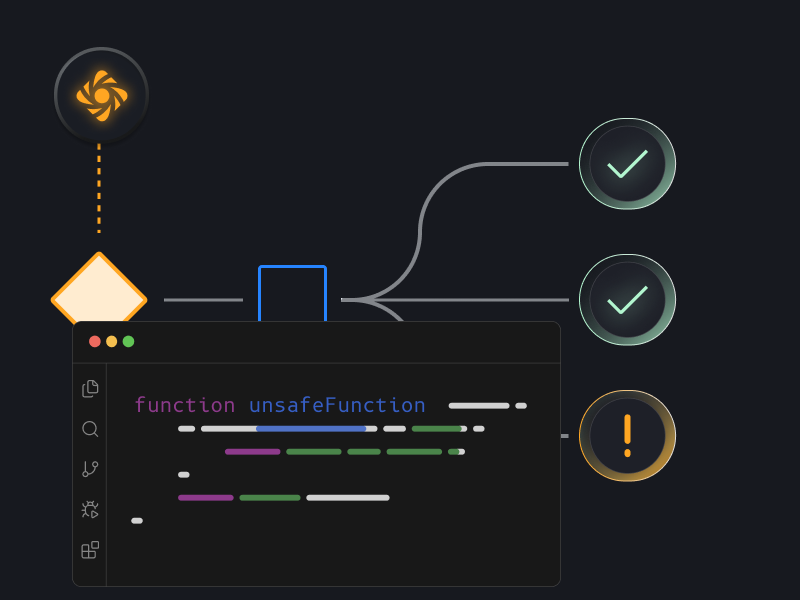
Attack Path Analysis
Identify potential attack paths for each detected risk
Security Control Enforcement
Verify that required security controls are implemented before code is approved or merged

See Prime Security in Action
Book a demo to see Prime in action



.png)



.png)



