Use Cases
Close Exploitable Attack Vectors Before Code Ships
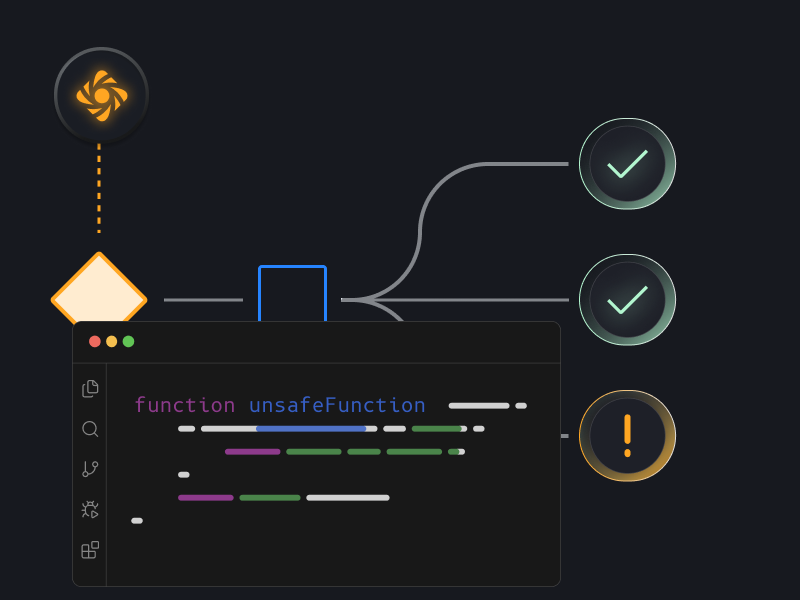
Let Prime Agents review every PR and repo against your architecture and cloud context - so you know which issues an attacker can exploit.
Key Benefits
Go beyond vulnerabilities, identifying multi step attack vectors
Reduce false positive rate by 80% compared to traditional code scanners
Key Benefits
Go beyond vulnerabilities, identifying multi step attack vectors
Reduce false positive rate by 80% compared to traditional code scanners

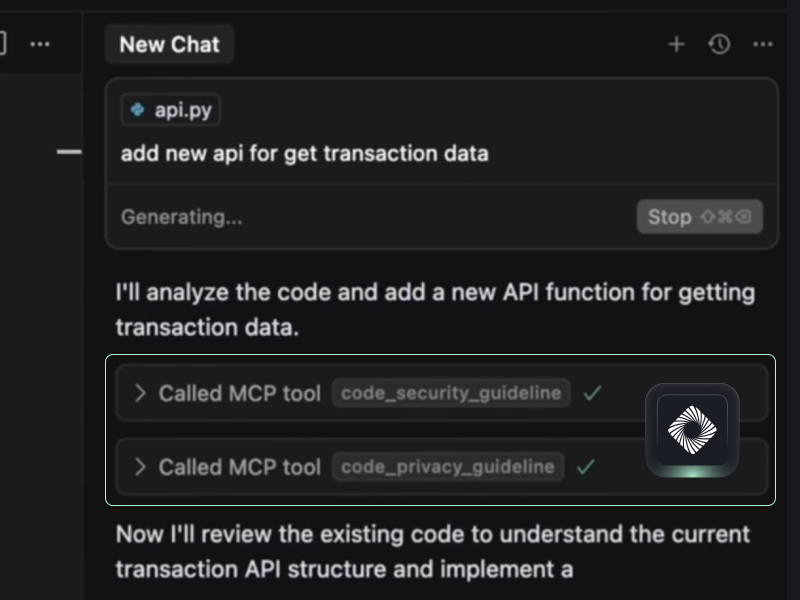
Bring the same security rigor directly into AI dev tools
Pull Request Monitoring
Monitor every pull request to ensure every change is evaluated before deployment
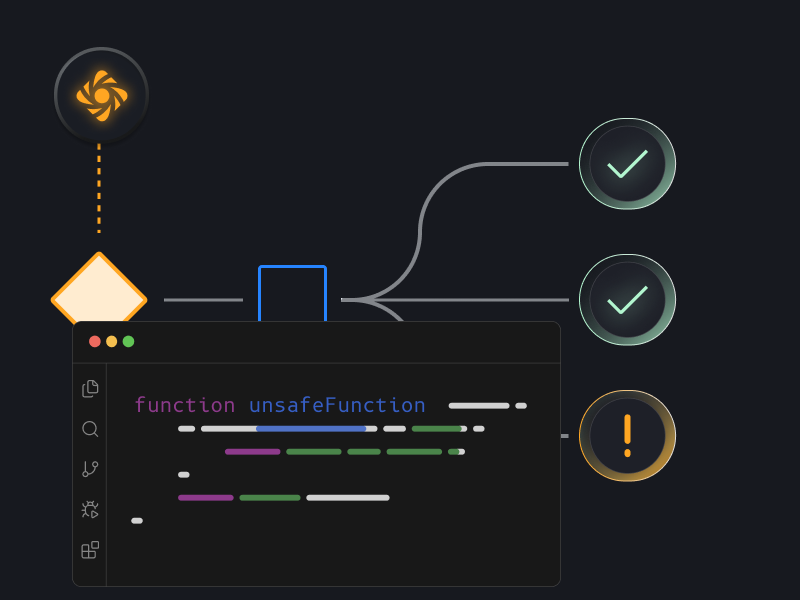
Attack Path Analysis
Identify potential attack paths for each detected risk
Security Control Enforcement
Verify that required security controls are implemented before code is approved or merged

Modern product security teams move their teams forward with Prime
See Prime Security in Action
Book a demo to see Prime in action





.png)
.png)