Product Security vs Application Security: Key Differences Explained
Your AppSec team closes vulnerabilities faster than ever, but the backlog never shrinks because the same design mistakes keep shipping. That's the gap between application security and product security: AppSec finds implementation bugs after code is written, while product security catches architectural flaws before anyone commits to a bad decision. If fewer than half your known vulnerabilities ever get fixed, the problem isn't remediation speed. It's that you're building things that require heavy remediation in the first place.
TLDR:
- Product security shapes designs before code is written; AppSec validates code after.
- Fixing design flaws post-release costs 15x more than catching them during design.
- Only 10-15% of planned work gets security review, leaving most risks undetected.
- Prime automates design reviews, expanding coverage to nearly 100% in under 20 minutes.
What Is Application Security
Application security secures software at the implementation layer: where code lives, where vulnerabilities hide, and where fixes get shipped. AppSec teams find and remediate weaknesses after design decisions have already been made.
The tooling is familiar to most security practitioners:
- SAST (static application security testing) scans source code for known vulnerability patterns
- DAST (runtime application security testing) probes running applications for exploitable flaws
- SCA (software composition analysis) flags risky open-source dependencies
AppSec is reactive by nature, not because AppSec teams aren't sharp, but because the work begins after architectural decisions are locked in. It validates implementation: if a developer writes an insecure authentication flow, AppSec catches it in review. If a third-party library carries a known CVE, SCA surfaces it.
The analogy that lands well internally is building a house. AppSec checks whether the walls are painted according to spec. It does not decide where the fire exits go before construction starts. That's a different job entirely.
TLDR: AppSec secures applications at the code and runtime level using tools like SAST, DAST, and SCA. It operates after design decisions are made, focusing on finding and fixing vulnerabilities in what's already been built.
What Is Product Security
Product security is what happens before anyone writes a line of code. Where AppSec validates what's been built, product security shapes what gets built and how. It's the discipline responsible for embedding security into the product lifecycle from ideation through deployment and end of life.
The scope is broader than any single application. Product security covers:
- Design-stage threat modeling and architecture reviews
- Supply chain risk across third-party components and integrations
- Cross-functional security requirements spanning multiple product surfaces
Most organizations realize this function exists only after they've felt its absence. Only about 10-15% of planned development work typically gets reviewed for security risk, meaning most design decisions ship without security review.
TLDR: Product security embeds security throughout the product lifecycle from design through end of life, covering design reviews, architectural decisions, and supply chain risks well before AppSec's tools come into play.
When Security Enters the Development Lifecycle
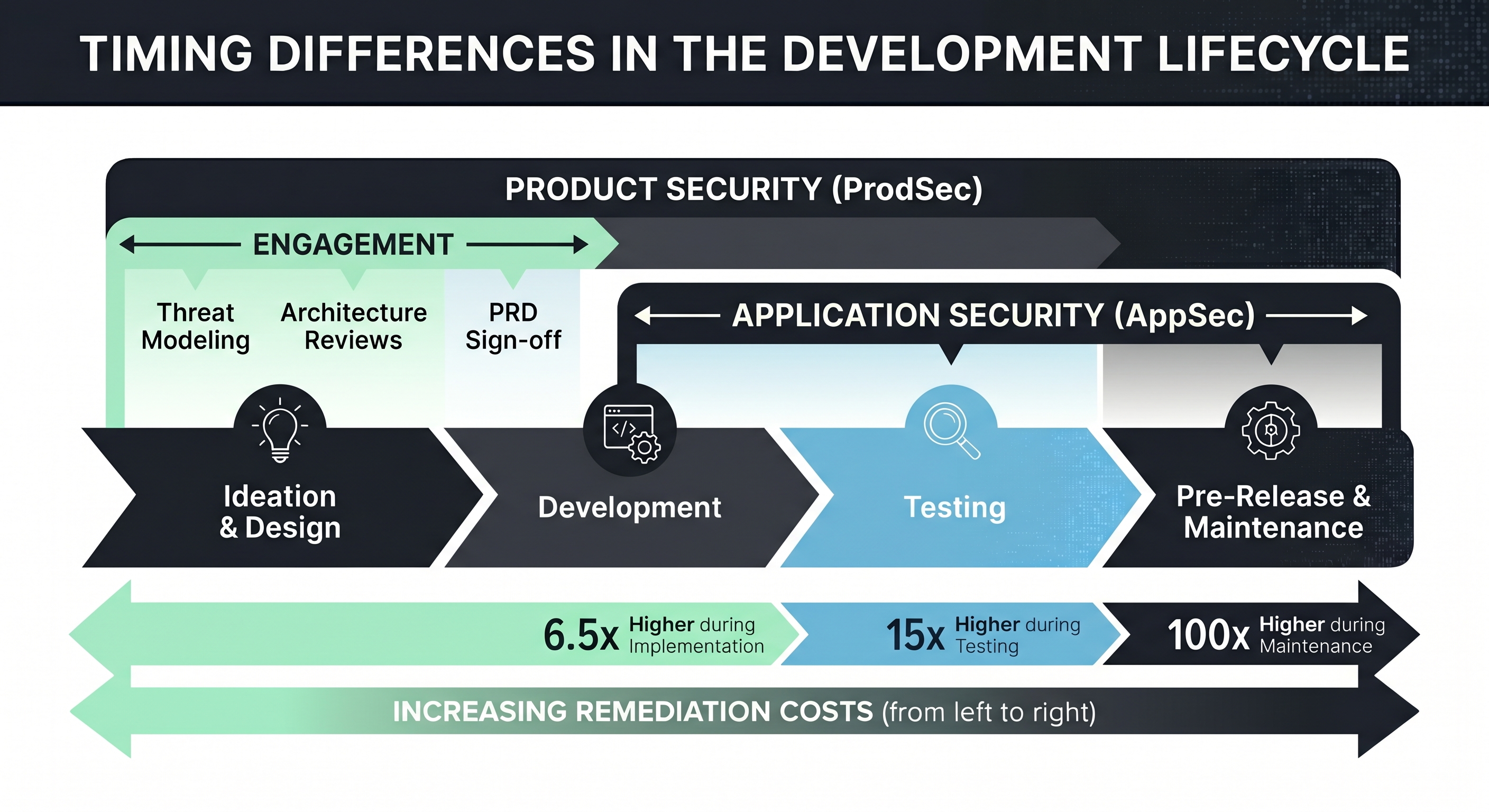
TLDR: Product security enters at ideation and design. AppSec enters at development and testing. The earlier security shows up, the cheaper and easier it is to fix what it finds.
Timing is where the two disciplines diverge most sharply. Product security engages at ideation and design, during threat modeling, architecture reviews, and PRD sign-off, before a single line of code is written. AppSec follows later, picking up during development, testing, and pre-release.
That gap matters more than it sounds. A flawed authentication architecture caught at the design stage is a conversation. Caught post-deployment, it's an incident. Research indicates that remediation costs are 6.5x higher during the implementation phase, 15x higher during testing, and 100x higher during maintenance. Product security exists, in part, to capture that savings before anyone commits to a bad decision.
Scope and Coverage Differences
AppSec and ProdSec enter the lifecycle at different times and cover different terrain entirely.
AppSec focuses on individual applications: the code, the runtime environment, the libraries, and the build pipeline. It's a component-level view, thorough within its boundaries, but bounded nonetheless. A vulnerability scanner doesn't care whether the API it's testing exposes data across three product lines or integrates with a third-party payment processor operating under PCI requirements.
ProdSec takes a systems-level view. The questions it asks are broader:
- How do this feature's data flows interact with existing infrastructure?
- What happens when a third-party integration changes its API behavior?
- Does this new component introduce supply chain risk across the entire product?
- Are the cloud services handling this data scoped and configured securely by design?
That difference in scope is why both disciplines can coexist in the same organization without overlap. One secures the parts. The other secures how the parts fit together, and what happens when one of them fails.
TLDR: AppSec secures individual apps at the component level. ProdSec covers the full ecosystem: hardware, APIs, cloud infrastructure, third-party integrations, and compliance requirements across the entire product surface.
Team Structure and Responsibilities
AppSec teams live close to engineering. They review pull requests, manage vulnerability scanners, triage findings from SAST and DAST tooling, and work alongside developers to close issues before release. The feedback loop is tight and the work is tactically focused.
Product security teams operate differently, pulling them into conversations with product management, compliance, legal, and even customer success. A product security engineer reviewing a new AI feature is asking whether it meets regulatory requirements, how it affects enterprise trust posture, and what downstream risk looks like if it ships with a flawed data model.
Application Security vs. Product Security Team Roles
Some key structural differences worth noting:
- Application Security: security engineers running SAST, DAST, and SCA tooling, code reviewers embedded in engineering sprints, and vulnerability management specialists tracking CVEs and remediation timelines.
- Product Security: security architects conducting design reviews and threat modeling, a head of product security reporting to the CISO, and cross-functional liaisons working with product, compliance, and customer-facing teams.
Product security functions skew heavier toward senior architects because the work requires judgment beyond tooling. Deciding whether a proposed architecture introduces unacceptable risk is a different skill than running a scanner.
TLDR: Application security teams embed with engineering to test and fix code. Product security teams operate cross-functionally, shaping security frameworks and working across product, compliance, and leadership.
Product Security Engineer Role and Career Path
Product security engineers sit at the intersection of security architecture, risk analysis, and product strategy. Where an application security engineer spends most of their day in code, a product security engineer is more likely to be in a design review, a threat modeling session, or a cross-functional meeting with product and engineering leadership.
The core skill set reflects that breadth:
- Threat modeling and architecture risk analysis
- Secure design patterns and framework knowledge (MITRE ATT&CK, NIST, STRIDE)
- Familiarity with product development lifecycles and agile workflows
- Communication skills to translate risk into business language
Career Progression
Entry-level roles typically start in application security or general security engineering. Practitioners who develop a taste for upstream, design-stage work tend to migrate toward product security over time. Senior roles lean heavily on security architecture experience, and the most senior individual contributors often function as de facto security architects for entire product lines.
TLDR: Product security engineers bridge security architecture and product strategy, requiring threat modeling skills, design-stage judgment, and cross-functional communication.
Risk Types Each Discipline Handles
The risks each discipline catches are as different as the phases they work in.
AppSec handles implementation-layer problems: SQL injection, cross-site scripting, insecure deserialization, misconfigured headers, and vulnerable dependencies. These are bugs introduced during development, catchable with scanners and code review.
Product security handles a different category entirely:
- Design flaws: an authentication model that's fundamentally broken before a single function is written
- Architectural vulnerabilities: data flows that expose sensitive information across trust boundaries by design
- Systemic risks: supply chain dependencies or third-party integrations that introduce risk at the ecosystem level
The distinction matters because design flaws can't be patched out. If an architecture routes unencrypted PII through an unsecured internal service, no SAST tool fixes that. It gets rebuilt or it ships broken.
TLDR: AppSec catches bugs and misconfigurations in code. Product security catches flawed designs, risky architectures, and systemic vulnerabilities before implementation makes them permanent.
How Product Security and Application Security Work Together
Neither discipline wins without the other. AppSec finds what slipped through. Product security tries to prevent it from slipping through in the first place. Organizations that treat them as competing priorities end up with gaps in both directions.
The handoff looks like this: product security defines the security requirements and architectural constraints before development begins. AppSec then validates that those requirements were actually implemented correctly. When coordinated, a flaw caught by SAST can inform the next design review. When siloed, the same class of vulnerability ships repeatedly because no one connected the pattern upstream.
Mature teams formalize this through shared frameworks and joint governance:
- Unified SDLC checkpoints where both functions sign off at different stages
- Shared vulnerability data that feeds back into design-stage decisions
- Cross-functional design reviews where AppSec input informs architectural choices
TLDR: Product security and AppSec cover different layers and work best when coordinated. Product security sets the design requirements; AppSec validates their execution. Together, they close the loop between intent and implementation.
Measuring Effectiveness and Success Metrics
AppSec and product security don't share KPIs because they don't share problems. Measuring one with the other's metrics tells you almost nothing useful.
AppSec success looks like:
- Vulnerability count trends over time
- Mean time to remediate (MTTR)
- Test coverage across code repositories
- CVE backlog reduction
Product security success looks different:
- Percentage of planned development work that received a design review
- Reduction in design rework caused by late-stage security findings
- Compliance audit pass rates and audit readiness posture
- Time to market for new features that cleared secure-design requirements
The coverage metric is worth sitting with. If only 10-15% of planned work gets reviewed, a product security team with zero vulnerabilities in queue isn't success. They're just not looking. Coverage is the floor everything else stands on.
What those metrics signal, together, is whether security is integrated or reactive. AppSec numbers tell you how well the organization remediates. Product security numbers tell you whether the organization is building things that need heavy remediation in the first place.
TLDR: AppSec measures vulnerability counts, MTTR, and test coverage. Product security measures design review coverage, compliance posture, and reduced rework. Each set reflects a different layer of organizational security health.
Common Challenges and Limitations
Both disciplines are harder to run well than org charts suggest.
AppSec teams deal with tool sprawl, scanner noise, and developer friction. The more tools you add, the more alerts pile up, and the less any single finding gets taken seriously. Alert fatigue is a genuine triage failure that lets real vulnerabilities age out in a backlog.
Product security faces a different wall: scale. Manual threat modeling depends on a handful of senior engineers who can't be in every design review. The result is that only 10-15% of planned work actually gets reviewed, and the other 85-90% ships without structured security input.
What makes both problems worse is the perception gap. While 81% of organizations say their security posture is strong, fewer than 48% of known vulnerabilities ever get remediated, according to Tenable. Confidence outruns execution by a wide margin.
How AI-Powered Development Is Changing the SDLC
AI agents are reshaping software architecture faster than any security review process was designed to handle. Where a sprint once moved at human pace, AI-assisted development compresses weeks of work into hours. The security functions built around that older cadence, weekly design reviews, manual code audits, quarterly threat model refreshes, were not designed for this velocity.
The result is not just more work. It is a fundamentally different risk profile. AI-generated code is expanding the attack surface faster than teams can scan it, compliance assumptions made last quarter are already stale, and the design decisions that product security exists to catch are now arriving in volume that manual review cannot absorb. Both disciplines feel this pressure, but in different ways.
What AI-Powered Development Means for AppSec
AI-generated code looks clean. It passes linters, follows style guides, and ships fast. It can also introduce subtle vulnerabilities that pattern-matching scanners miss, because the patterns themselves are new. AppSec teams are watching CVE backlogs grow faster than they can close tickets, not because remediation slowed down, but because the code surface is expanding at a pace manual review was never built to match.
- Developers using AI coding assistants do not always signal what changed or why. Pull request descriptions get thinner, commit messages reference the prompt rather than the intent, and the context AppSec needs to prioritize findings is harder to reconstruct after the fact.
- AI-generated code can produce vulnerability classes that trained scanners have limited coverage for, because the patterns are novel or the context is stripped away.
- Alert fatigue, already a structural problem, compounds when code volume and findings scale nonlinearly while security headcount stays flat.
The throughput problem AppSec already faced gets harder when the denominator keeps growing. Teams that were stretched at a 50:1 developer-to-security ratio are now effectively operating at much higher ratios, without any change to the org chart.
What AI-Powered Development Means for Product Security
For product security, the challenge is architectural. AI agents do not just write functions. They propose integrations, suggest third-party services, and draft entire system designs. When a developer accepts a suggestion that routes sensitive data through an external API, that is an architectural decision made without a design review. Multiply that by every developer on every team, every day, and the 10-15% design review coverage problem gets harder to close, not easier.
- Threat models written last quarter may already be stale. Architectures shift between standups when AI is accelerating feature development.
- Third-party integrations and cloud service configurations, the supply chain risks product security is responsible for evaluating, are being introduced faster than any manual review process tracks.
- The design-stage conversation that product security exists to have is increasingly happening between a developer and an AI assistant, with no security input in the room.
The 85-90% of planned work that does not receive a design review was already a coverage problem. AI-assisted development does not improve that number. It raises the stakes attached to each missed review.
TLDR: AI-powered development accelerates the exact risks both AppSec and ProdSec were built to address. AppSec teams face higher code volume, thinner commit context, and growing backlogs. Product security teams face architectural decisions happening faster than design reviews can follow, with threat models going stale before the ink is dry.
When to Invest in Product Security Versus Application Security
AppSec is the baseline. Any organization shipping software needs it. Product security becomes the priority when your products grow complex enough that architecture decisions carry real downstream risk.
A few signals that product security investment is overdue:
- Design rework is eating sprint capacity because security catches issues too late
- Enterprise customers or regulators are asking about your secure development practices
- Your developer-to-security ratio has crossed 50:1 and reviews are not keeping pace
- You're shipping AI features or third-party integrations with no formal design review process
Early-stage companies typically start with AppSec, add a product security function around Series B or C, and formalize it once regulatory pressure or customer scrutiny makes informal processes unsustainable.
TLDR: AppSec first, always. Add product security when product complexity, compliance requirements, or enterprise trust expectations outgrow what reactive tooling can cover.
How Prime Security Automates Product Security at Scale
The scaling challenges outlined throughout this post aren't unsolvable. They're just unsolvable with manual processes.
Prime continuously scans Jira, Confluence, and connected planning tools to surface design-stage risks across all planned development work, not the 10-15% that fits into a security team's calendar. Acting as an Agentic Security Architect, Prime automates design reviews, threat modeling, and risk analysis, so coverage expands without adding headcount.
That continuous coverage matters most when AI-assisted development is accelerating the pace of architectural decisions. When developers are accepting AI-suggested integrations, routing data through new third-party APIs, and drafting system designs faster than any manual review cadence was built to handle, the 85-90% design review gap gets harder to close without automation. Prime keeps pace with that velocity by scanning planning artifacts as they are created and updated, not on a weekly or quarterly review schedule. Threat models stay current because Prime is continuously re-evaluating them, not waiting for a senior engineer to have a free afternoon.
The output is consistent, auditable, and architect-level in reasoning. Reviews that previously took days run in under 20 minutes. Findings land directly in engineering workflows, not in a spreadsheet no one checks.
If your team is the bottleneck between design and deployment, that's worth fixing before the next release cycle.
TLDR: Prime automates product security design reviews at scale, expanding coverage from 10-15% to nearly 100% of planned work by integrating directly into Jira and Confluence. That continuous scanning is especially critical when AI-assisted development is compressing weeks of architectural decisions into hours, without slowing engineering down.
Final Thoughts on Product Security Versus Application Security
Understanding product security versus application security changes how you allocate your security resources and where you intervene in the development lifecycle. AppSec finds the bugs, but product security stops entire classes of vulnerabilities from becoming architecturally possible. If fewer than half your known vulnerabilities get remediated and only 10-15% of planned work receives design review, you're solving the wrong bottleneck. Prime brings architect-level design reviews to every Jira ticket, every PRD, and every planned feature before engineering writes a line of code.
FAQ
Product security vs application security: what's the actual difference?
Product security shapes design decisions before code is written, while application security validates the code itself. Product security asks "where do the fire exits go?" during architectural planning; AppSec checks whether the walls were built to spec after construction starts.
What skills do you need to become a product security engineer?
You need threat modeling and architecture risk analysis skills, familiarity with frameworks like MITRE ATT&CK and STRIDE, understanding of product development lifecycles, and the ability to translate security risk into business language. Most product security engineers start in AppSec roles and move upstream once they develop design-stage judgment.
Can product security reviews actually keep up with AI-assisted development?
Manual reviews can't, which is why most organizations only review 10-15% of planned work. AI-powered platforms can continuously scan development plans and automate design reviews, expanding coverage to nearly 100% without adding headcount or slowing engineering velocity.
When should a company invest in product security versus just doing AppSec?
Invest when design rework is eating sprint capacity because security catches issues too late, when your developer-to-security ratio exceeds 50:1, or when enterprise customers start asking about your secure development practices. AppSec is the baseline; product security becomes critical when architectural decisions carry real downstream risk.



.png)



.png)

