Context is King: Finding Vulnerabilities Was Never the Hard Part
TL;DR
Anthropic's Claude Code Security launch (which tanked cybersecurity stocks) is impressive but misses the real problem — enterprise security teams are already drowning in vulnerability alerts, not starved for them. Finding bugs was never the bottleneck; knowing which ones actually matter to your specific organization is. Prime's Security Context Engine turns raw scanner findings into actionable priorities by layering in your architecture, compliance obligations, and past decisions. Better AI scanners will just generate more noise without that layer. Context is the moat; detection is becoming a commodity.
On Feb 19th, 2026, the cyber earth shook! The cyber security market lost billions in a single afternoon. JFrog dropped 25%. CrowdStrike fell 8%. And all because Anthropic launched Claude Code Security.
Here’s what I find fascinating: the market panicked about the wrong thing.
Claude Code Security is genuinely impressive, an AI model that reasons about code like a security researcher, finds zero-days that survived decades of expert review, and suggests patches for human approval. That’s a HUGE milestone. But the breathless headlines about AI “replacing” cybersecurity miss a fundamental truth:
Finding vulnerabilities has never been the hard part. Knowing what to do about them is.
Better scanners don’t solve the real problem
What Anthropic built matters. Reasoning-based vulnerability discovery is a genuine leap, and static analysis becoming embedded in AI coding platforms is the right direction for the industry.
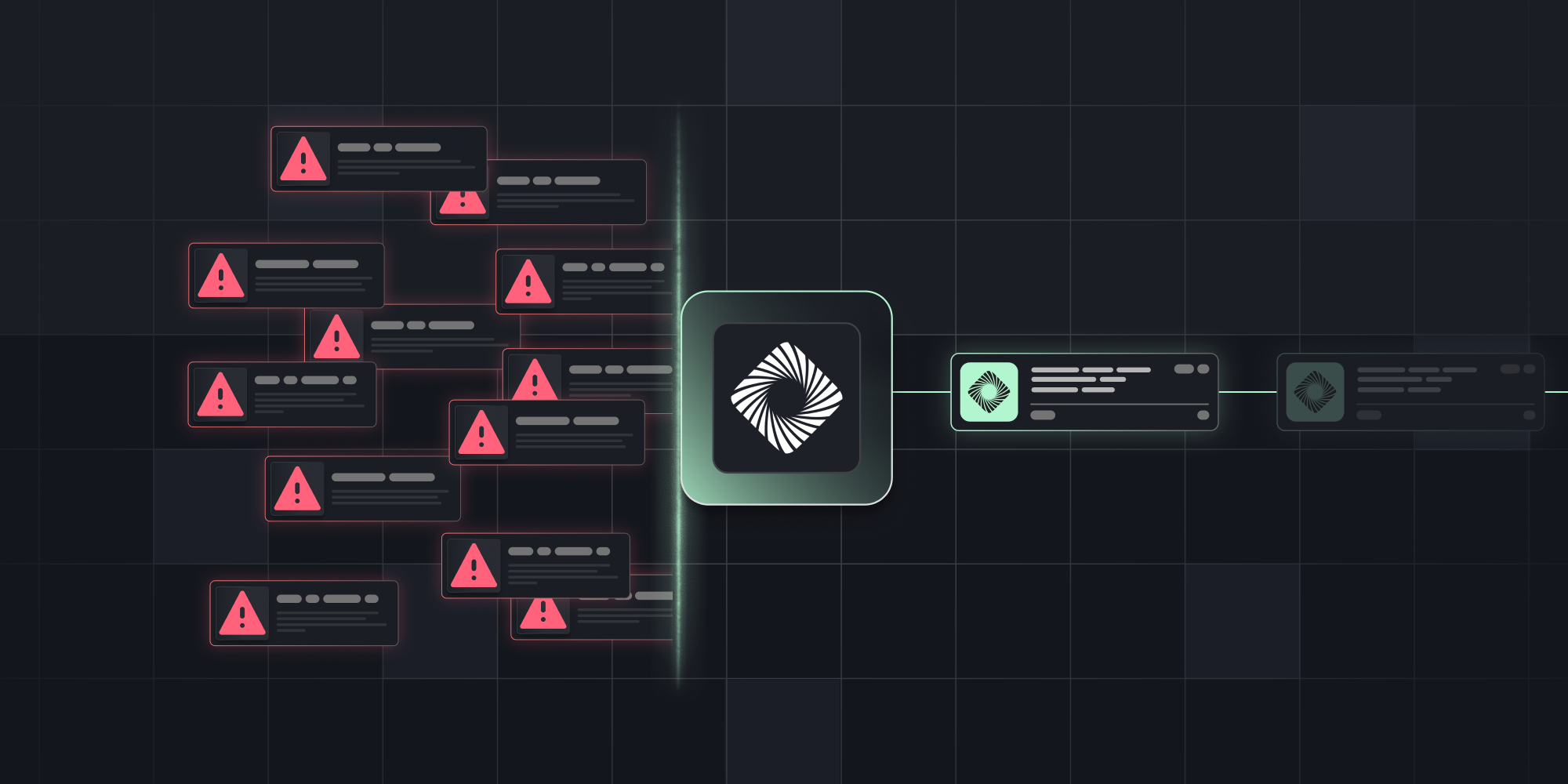
But enterprise security teams aren’t starved for findings, they’re drowning in them. SAST, DAST, SCA, container scanners, each one generating alerts, none capable of answering the only question that matters:
“Should I care about this one?”
That’s a context question. And it eats 80% of a security team’s time.
Claude Code Security is a dramatically better way to find code-level vulnerabilities. But it doesn’t know your architecture, your compliance obligations, or the security exceptions your architect approved last quarter. Without that context, even the most brilliant finding is just another alert in the queue.
Same vulnerability, two completely different realities
Let me make this concrete. Imagine Claude Code Security finds an insecure direct object reference (IDOR) in your codebase. A user can manipulate an API parameter to access another user’s data. The scanner flags it as high severity and even suggests a patch. Impressive work.
Now what?
Without business context, your security team sees one more high-severity finding in a backlog of 200. An engineer spends 45 minutes triaging; pulling up architecture diagrams, pinging the team lead on Slack, digging through Confluence. They eventually discover it’s an internal admin tool used by six people, accessible only through a VPN behind SSO. The IDOR is real, but the blast radius is tiny. Forty-five minutes gone. Multiply that by 30 findings a day.
That’s not security engineering. That’s archaeology.
With organizational context, the same IDOR gets instantly enriched by Prime’s Security Context Engine: Checkout Service, Tier 1, internet-facing, PCI-DSS. The design review eight weeks ago recommended object-level authorization checks and was linked to a Jira ticket which was deprioritized after a production incident. The feature team ships in six days.
Same vulnerability. First scenario: 45 minutes to figure out whether to care. Second: the team acts within seconds due to a critical finding, compliance obligation, known fix, tight deadline.
That’s the difference context makes. A fundamentally different operating model.
This is exactly why we built Prime
Prime’s Security Context Engine is an organizational context graph. A living map of your security architecture decisions, risk exceptions, and compliance requirements. The institutional memory that turns raw findings into actionable intelligence.
Any scanner can tell you what’s wrong. Prime tells you why it matters to your organization, and what to do about it.
Detection is maturing. Context is just getting started.
The Claude Code Security launch validates the thesis we’ve been building around since day one.
Scanning and operationalization tools play a vital role in any mature security program. But detection is converging fast. When a frontier AI model can discover 500 zero-days with no custom scaffolding, the race to find more bugs has a ceiling.
What doesn’t have a ceiling is organizational knowledge. That knowledge compounds with every design decision processed, every review completed, every exception documented. It deepens with time, and new entrants can’t shortcut it.
The three-layer future of product security
Here’s how I see the product security stack evolving:
Layer 1: Design-stage intelligence. Before code is written, understand the security implications of what you’re about to build. This is Prime’s core, automated security and privacy design reviews with architect-level guidance in real time.
Layer 2: Code-level scanning. Once code is written, scan it for vulnerabilities. Claude Code Security, traditional SAST/DAST tools, SCA analyzers live here. This layer is getting dramatically better and cheaper.
Layer 3: Runtime protection and response. Endpoint detection, identity management, network security. CrowdStrike, Cloudflare, Okta and the likes were never threatened by a code scanner, and the market selloff was, as Barclays put it, “illogical.”
The insight is that Layer 1 makes Layer 2 dramatically more useful. When you understand your architecture and design decisions before code is written, every finding from a scanner arrives pre-contextualized. You’re not triaging from scratch, you’re confirming or updating what you already know.
And the benefits to layer 3 I’ll leave to a separate post…
The question security leaders should actually be asking
Anthropic’s Claude Code Security is a genuinely exciting development for defenders. But better scanners mean more findings. More findings without context means more noise. And the real question this launch should prompt isn’t “will AI replace my security tools?” it’s “am I positioned to absorb the coming flood of AI-generated findings?”
The organizations that thrive won’t be the ones with the best scanners, they’ll be the ones that can instantly contextualize any finding against their specific risk posture and act on what actually matters.
Scanners find. Context decides.
And context is king.





.png)
.png)

